| Objective: Spare Key | Difficulty Level: 1 |
|---|---|
| Help Goose Barry near the pond identify which identity has been granted excessive Owner permissions at the subscription level, violating the principle of least privilege. | Location: The Pond |
Solution Overview
Conduct reconnaisance of an Azure tenant looking for for interesting files that might contain valuable information. The $web directory was explored for configuration files. A terraform file contained a long-lived SAS migration token.
| Activity | Primary Tactic | MITRE ATT&CK Technique ID | MITRE ATT&CK Technique Name |
|---|---|---|---|
| Discovering SAS key in Azure Storage | Reconnaissance | T1526 | Cloud Service Discovery |
Detailed Solution
Click to expand
Start by listing all resource groups:
az group list -o table

Next get a listing of storage accounts:
az storage account list --resource-group rg-the-neighborhood -o table
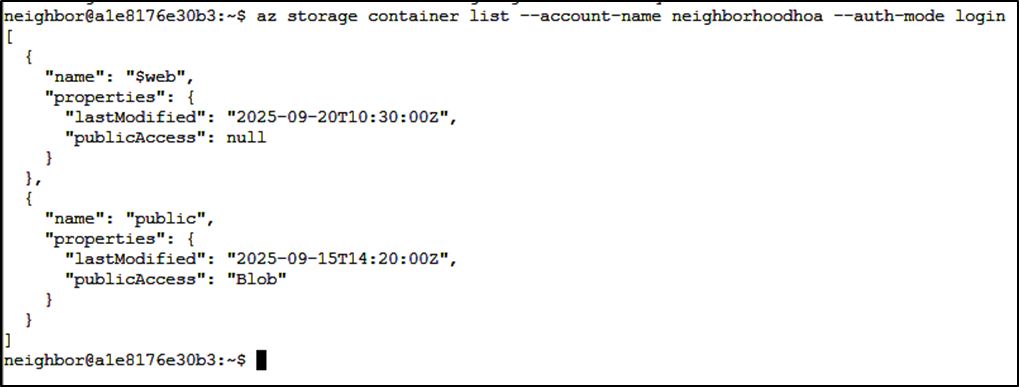
Examining the files in the static website container:
az storage blob list --container-name '$web' account-name neighborhoodhoa --auth-mode login

The metadata WARNING: LEAKED_SECRETS looks promising. Download the file to review:
az storage blob download \
--account-name neighborhoodhoa \
--container-name '$web' \
--name 'iac/terraform.tfvars' \
--file terraform.tfvars \
--auth-mode login

Tools Reference
| Tools Used | Tool Version |
|---|---|
| Azure CLI | N/A |
Hints Reference
| Provided By | Hint |
|---|---|
| Santa | This terminal has built-in hints! |
Acknowledgements
| Provided By | Notes |
|---|---|
| none | none |
